Throughout today's interconnected globe, where data is the lifeline of companies and people alike, cyber protection has actually ended up being extremely important. The boosting elegance and frequency of cyberattacks demand a robust and proactive strategy to securing delicate details. This short article explores the important aspects of cyber protection, with a specific concentrate on the internationally recognized criterion for details safety and security management, ISO 27001.
The Evolving Landscape of Cyber Threats:.
The digital world is frequently advancing, and so are the threats that hide within it. Cybercriminals are coming to be progressively skilled at exploiting susceptabilities in systems and networks, posing significant dangers to organizations, federal governments, and individuals.
From ransomware attacks and information breaches to phishing rip-offs and distributed denial-of-service (DDoS) attacks, the range of cyber dangers is vast and ever-expanding.
The Significance of a Proactive Cyber Protection Technique:.
A reactive approach to cyber security, where organizations just attend to hazards after they occur, is no longer sufficient. A positive and extensive cyber security method is essential to alleviate risks and shield valuable properties. This includes implementing a combination of technical, business, and human-centric measures to secure info.
Introducing ISO 27001: A Framework for Information Safety And Security Administration:.
ISO 27001 is a globally recognized criterion that sets out the requirements for an Info Safety And Security Management System (ISMS). An ISMS is a organized technique to taking care of sensitive information to ensure that it stays safe. ISO 27001 offers a framework for establishing, executing, maintaining, and consistently boosting an ISMS.
Trick Elements of an ISMS based upon ISO 27001:.
Risk Evaluation: Identifying and examining prospective dangers to details safety and security.
Safety And Security Controls: Executing ideal safeguards to alleviate identified dangers. These controls can be technological, such as firewall programs and security, or organizational, such as plans and treatments.
Management Review: Consistently assessing the efficiency of the ISMS and making necessary improvements.
Internal Audit: Conducting inner audits to make sure the ISMS is operating as intended.
Consistent Enhancement: Constantly looking for means to enhance the ISMS and adapt to evolving risks.
ISO 27001 Qualification: Demonstrating Dedication to Information Safety And Security:.
ISO 27001 Certification is a official acknowledgment that an company has actually carried out an ISMS that satisfies the needs of the standard. It demonstrates a commitment to details safety and offers guarantee to stakeholders, consisting of consumers, companions, and regulatory authorities.
The ISO 27001 Audit Process:.
Achieving ISO 27001 Accreditation involves a rigorous audit procedure performed by an certified accreditation body. The ISO 27001 Audit evaluates the organization's ISMS versus the requirements of the criterion, guaranteeing it is properly carried out and maintained.
ISO 27001 Conformity: A Continuous Trip:.
ISO 27001 Compliance is not a single success yet a constant trip. Organizations has to consistently assess and upgrade their ISMS to guarantee it stays reliable in the face of evolving threats and business demands.
Finding the Cheapest ISO 27001 Certification:.
While price is a element, picking the " least expensive ISO 27001 qualification" need to not be the key chauffeur. Focus on locating a respectable and certified accreditation body with a proven record. A detailed due persistance process is important to guarantee the certification is reputable and important.
Advantages of ISO 27001 Accreditation:.
Improved Info Safety And Security: Reduces the risk of information breaches and various other cyber safety events.
Improved Business Reputation: Demonstrates a dedication to info safety and security, boosting depend on with stakeholders.
Competitive Advantage: Can be a differentiator in the market, especially when managing delicate details.
Compliance with Regulations: Helps organizations meet regulatory needs associated with information defense.
Raised Effectiveness: Improves info security procedures, bring about boosted performance.
Beyond ISO 27001: A Alternative Approach to Cyber Protection:.
While ISO 27001 gives a useful structure for details safety and security management, it is very important to remember that cyber safety is a complex difficulty. Organizations ought to adopt a all natural approach that incorporates various elements, including:.
Staff certification Member Training and Understanding: Educating workers regarding cyber safety ideal practices is essential.
Technical Protection Controls: Applying firewall softwares, breach discovery systems, and other technical safeguards.
Data File encryption: Protecting delicate information through encryption.
Occurrence Feedback Preparation: Creating a plan to respond properly to cyber security incidents.
Vulnerability Administration: On a regular basis scanning for and dealing with vulnerabilities in systems and networks.
Verdict: Building a Secure Digital Future:.
In an increasingly interconnected whole world, cyber security is no longer a high-end yet a need. ISO 27001 gives a durable framework for organizations to develop and maintain an effective ISMS. By welcoming a aggressive and detailed technique to cyber safety and security, companies can safeguard their useful details assets and build a safe and secure electronic future. While accomplishing ISO 27001 compliance and accreditation is a significant action, it's essential to keep in mind that cyber safety is an recurring process that calls for constant caution and adjustment.
 Mason Gamble Then & Now!
Mason Gamble Then & Now!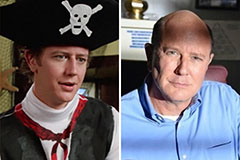 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Brandy Then & Now!
Brandy Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now!